Signet MCP Server
Cryptographic action receipts for AI agents. Signs every MCP tool call with Ed25519, hash-chained audit log. 3 lines of code to integrate.
Documentation
Signet
Don't just log agent actions. Prove them.
Cryptographic receipts for every AI agent tool call — signed, hash-chained, offline-verifiable. Independent of any provider.
TypeScript packages:
@signet-auth/core ·
@signet-auth/mcp ·
@signet-auth/mcp-server ·
@signet-auth/mcp-tools ·
@signet-auth/node ·
@signet-auth/vercel-ai
▶ Try the live demo — sign a tool call in your browser, change a field, and watch verification fail. (mirror: GitHub Pages)
▶ Walkthrough: signing, audit log, and verification · ▶ Demo: execution boundary & MCP integration
Single-host pilot flow: sign every tool call, hand off a signed evidence bundle, re-verify on any machine — no signet keystore required. Pilot runbook →
Your AI agent just placed an order, deleted a row, sent an email, merged a PR. Can you prove exactly what it did — to an auditor, a customer, or yourself after an incident?
Signet is the independent verification layer for agent actions. Every tool call gets a signed receipt that anyone can verify offline, without trusting the platform that hosted the agent or the vendor that stored the logs.
Your agents run on their infrastructure. The proof belongs to you.
Why Not Just Logs?
Traditional logs tell you what a platform says happened. They're mutable, provider-dependent, and unverifiable without trusting the party that wrote them.
Signet receipts are different. Modify any field — tool name, parameters, timestamp, signer — and the Ed25519 signature breaks. Delete or reorder entries and the SHA-256 hash chain breaks. Verification requires only the public key. No network call, no API, no login.
| Ordinary logs | Signet receipts |
|---|---|
| Provider says it happened | Anyone can verify it, offline |
| Mutable after the fact | Signature breaks on tamper |
| No ordering proof | Hash chain breaks on delete/reorder |
| Trust the log host | Verify with the public key |
| One-sided claim | Bilateral co-signing available |
Use logs for observability. Use Signet when you need evidence.
Who Is This For?
- MCP builders — wrap any MCP server with
signet proxy, sign everytools/call, no code changes - Security / compliance teams — tamper-evident audit trail that satisfies EU AI Act Art. 12, SOC 2 CC7.2, ISO 27001 A.8.15
- Enterprise agent platforms — prove what the agent did, who authorized it, which policy was in force
- Framework users — LangChain, CrewAI, Claude Code, Codex, OpenAI Agents, Vercel AI SDK — all supported
- Agent-to-agent deployments — bilateral co-signing when both sides hold keys
If a tool call cannot be verified independently, it should not be trusted unconditionally. This matters when an auditor asks for proof, when an incident happens on infrastructure you don't control, or when the question isn't "what does the console say" but "what actually happened."
Each agent gets an Ed25519 identity. Every tool call can be signed, appended to a hash-chained audit trail, verified offline or before execution, co-signed by the server, bound to a delegation chain, and optionally bound to a policy decision.
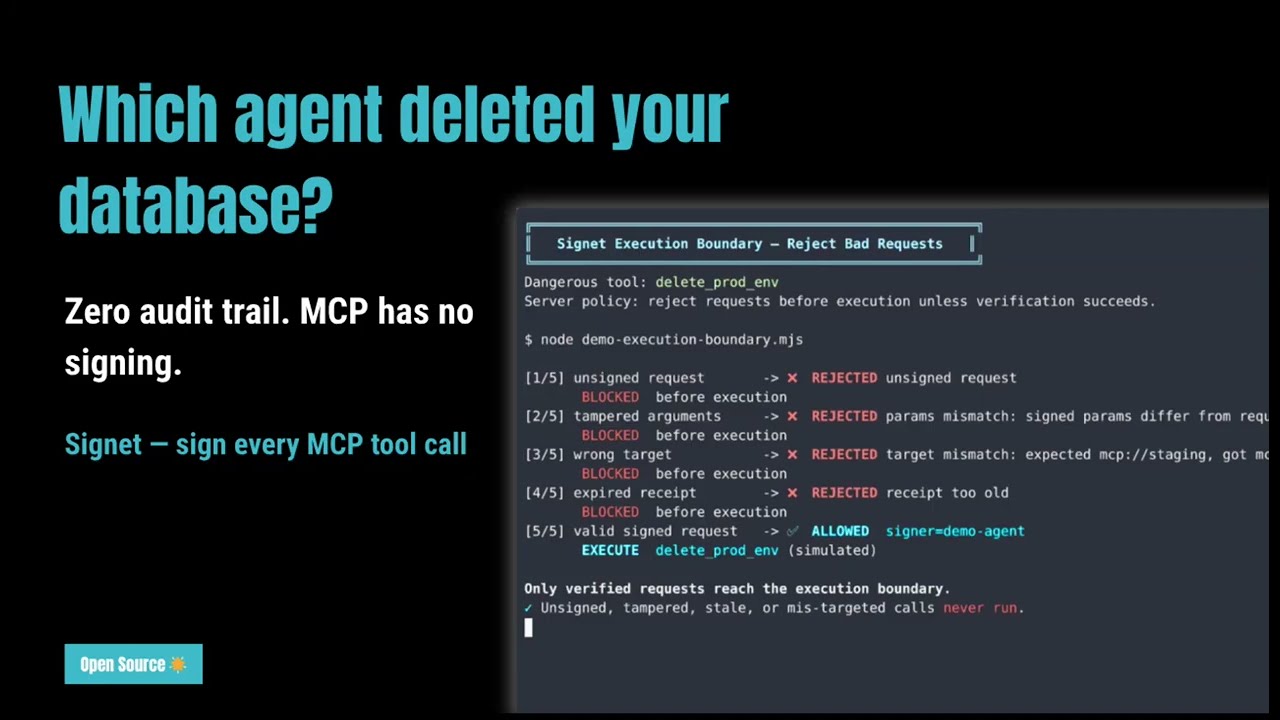
The video above shows the full flow. The SVG below shows the CLI signing details, or jump to See It Reject Bad Requests to watch the server block bad requests before they run.
This first demo shows signing + audit receipts. See also the MCP flow diagram.
What Signet Adds
Signet adds a lightweight trust layer for agent actions:
- Sign every tool call with the agent's cryptographic key
- Verify requests offline or at the execution boundary before they are trusted
- Proxy any MCP server transparently — sign requests without touching agent or server code, with local bilateral audit co-signing in the proxy path
- Co-sign server responses with bilateral receipts when you control both sides
- Trace multi-step workflows by linking receipts with
trace_idandparent_receipt_id - Authorize agents with scoped delegation chains that prove who allowed the action
- Attest policy by embedding a signed
PolicyAttestationwhen a YAML policy is satisfied - Inspect locally with an append-only audit log and dashboard, no hosted control plane required
What's New In 0.9
- MCP proxy:
signet proxy --target <cmd> --key <name>— drop Signet in front of any MCP server as a transparent stdio proxy. No changes to the agent or server required. Signs everytools/calland appends bilateral co-signatures to the local audit path; client-visible bilateral response handling is stronger through integrated transport/server helpers. - Trace correlation:
trace_idandparent_receipt_idfields onActionlink receipts across multi-step workflows into a causal chain. Both fields are part of the signed payload — tampering invalidates the signature. - Policy engine:
signet sign --policy policy.yamlenforces policy before signing and binds the decision into the receipt. The proxy also respects--policy, blocking denied calls before they reach the server while producing signed bilateralrejected/requires_approvaloutcomes and a hash-chainedpolicy_violationaudit record. - Delegation chains:
signet delegate ...produces v4 receipts that prove who authorized the agent and what scope it had. - Local dashboard:
signet dashboardshows timeline, chain integrity, signature health, and delegated vs direct activity. - Broader integrations: official Claude Code plugin, Codex plugin, MCP middleware, Python SDK, and Vercel AI SDK callbacks.
Compliance
Signet provides the technical controls that auditors look for when assessing AI agent operations. See the full Compliance Mapping for details.
| Framework | What Signet Addresses |
|---|---|
| SOC 2 Type II | Signed audit trail (CC7.2), tamper detection (CC7.3), role-based scope (CC6.3), authorization proof (CC8.1) |
| ISO 27001 | Event logging (A.8.15), access control (A.5.15), authentication (A.5.17), configuration management (A.8.9) |
| EU AI Act | Article 12 record-keeping: event logging, traceability, identification, integrity |
| DORA | ICT incident logging (Art. 17), third-party risk evidence (Art. 28-30), audit trail integrity |
| NIST AI RMF | Govern (delegation chains), Map (signed receipts), Measure (audit queries), Manage (policy engine) |
Signet is a tool, not a certification. It provides controls that support compliance — your deployment and configuration determine compliance posture.
Try It In 30 Seconds
pip install signet-auth
from signet_auth import SigningAgent
agent = SigningAgent.create("my-agent", owner="team")
receipt = agent.sign("github_create_issue", params={"title": "fix bug"})
assert agent.verify(receipt)
print(receipt.id)
Why Star This Repo?
Signet is building a new category: verifiable tool-call receipts for AI agents. Starring isn't just a bookmark — it helps push cryptographic evidence for agent actions into the ecosystem so regulated industries, enterprise platforms, and framework users don't have to roll their own.
- Working with Microsoft Agent Governance Toolkit (example merged in PR #1196)
- Named contributor in LangChain's ComplianceBackend RFC (#35691)
- Conformance work toward the IETF draft-farley-acta-signed-receipts spec
- Maps to NIST NCCoE's four pillars for AI agent identity and authorization (Q4 2026 Interoperability Profile)
If you're building agents that need to survive an audit, an incident, or a third party asking "prove it" — star the repo, try it, open an issue.
If you're new, start with one of these five paths:
Choose Your Path
- Claude Code: Best for the fastest first run in a coding agent. Run
/plugin install signet@claude-plugins-officialin Claude Code. In 5 minutes you'll have signed tool calls and a local audit log at~/.signet/audit/. - Codex CLI: Best for signing Bash tool calls in Codex. Copy
plugins/codex/into~/.codex/plugins/signetand add onePostToolUsehook. In 5 minutes you'll have signed Bash actions in Codex using the same audit trail. - Python SDK: Best if you want receipts inside LangGraph, LlamaIndex, OpenAI Agents, CrewAI, or your own tool runner. Start with
SigningAgent.create(...)and add framework hooks only where you need them. - MCP clients: Best if you control an MCP client or transport. Wrap your transport with
new SigningTransport(inner, secretKey, "my-agent"). In 5 minutes you'll have signedtools/callrequests with receipts inparams._meta._signet. - MCP servers: Best if you want verification before execution. Call
verifyRequest(request, {...})in your tool handler. In 5 minutes you'll have signer, freshness, target-binding, and tool/params checks at the execution boundary.
See It Reject Bad Requests
Run the shortest execution-boundary demo:
cd examples/mcp-agent
npm run execution-boundary-demo
Prefer motion? Download the MP4 or GIF.
See examples/mcp-agent/demo-execution-boundary.mjs for the demo source.
Delegation Chains: Who Authorized This Agent?
Signet receipts prove what happened. Delegation chains prove who allowed it.
A root identity (human or org) cryptographically delegates scoped authority to an agent. Permissions can only narrow, never widen. The agent's v4 receipt carries the full proof of authorization.
Owner (alice) → Agent A (tools: [Bash, Read], max_depth: 0)
↓
v4 Receipt: tool=Bash, authorization.chain proves alice → Agent A
# Create a delegation token (expires in 24 hours)
signet delegate create --from alice --to deploy-bot --to-name deploy-bot \
--tools Bash,Read --targets "mcp://github" --max-depth 0 --ttl 24h
# Sign with authorization proof (v4 receipt)
signet delegate sign --key deploy-bot --tool Bash \
--params '{"cmd":"git pull"}' --target "mcp://github" --chain chain.json
# Verify: signature + chain + scope + root trust
signet delegate verify-auth receipt.json --trusted-roots alice
Best practice: Use short-lived delegations (
--ttl 1h,--ttl 24h) instead of long-lived or non-expiring tokens. If an agent is compromised, the delegation expires automatically. Re-issue tokens as needed. This is the same pattern used by short-lived JWTs and X.509 certificates.
Or in Python:
from signet_auth import sign_delegation, sign_authorized, verify_authorized
# Delegation functions accept JSON strings for scope, chain, and receipts
token_json = sign_delegation(root_key_b64, "alice", agent_pubkey_b64, "bot", scope_json)
receipt_json = sign_authorized(agent_key_b64, action_json, "bot", f"[{token_json}]")
scope_json = verify_authorized(receipt_json, [root_pubkey_b64])
Policy Attestations: Was This Allowed?
Signet can enforce a YAML policy before signing. When an action is allowed, the signed receipt carries a PolicyAttestation proving which policy hash, rule, and decision were in force.
version: 1
name: production-agents
default_action: deny
rules:
- id: allow-read
match:
tool: Read
action: allow
- id: deny-rm-rf
match:
tool: Bash
params:
command:
contains: "rm -rf"
action: deny
reason: destructive command
signet policy validate policy.yaml
signet policy check policy.yaml --tool Bash --params '{"command":"rm -rf /"}'
signet sign --key deploy-bot --tool Read \
--params '{"path":"README.md"}' --target "mcp://github" --policy policy.yaml
Denied actions fail before a receipt is produced. Allowed actions produce a receipt whose signed payload proves the policy decision.
When Teams Reach For Signet
- You need a tamper-evident audit trail for coding agents, MCP tools, or CI automation
- You want to prove which agent requested an action and who authorized it after an incident
- You need receipts that can be verified offline without depending on a hosted service
- You want lightweight policy enforcement before signing without adding a proxy to your stack
What Signet Is And Isn't
- Signet is a trust layer for agent actions: signing, audit, verification, delegation, and policy attestation
- Signet is designed to fit into existing agent stacks with SDKs, plugins, and MCP middleware
- Signet can reject unsigned, stale, replayed, or mis-targeted MCP requests before execution
- Signet can deny actions before signing when you provide a policy file
- Signet is not a hosted gateway, always-on control plane, or replacement for sandboxing and least-privilege design
Install
# CLI
cargo install signet-cli
# Python
pip install signet-auth
# TypeScript (MCP middleware)
npm install @signet-auth/core @signet-auth/mcp
# TypeScript (MCP server verification)
npm install @signet-auth/mcp-server
# TypeScript (Node local audit/operator helpers)
npm install @signet-auth/node
# TypeScript (Vercel AI SDK middleware)
npm install @signet-auth/vercel-ai
# TypeScript (standalone MCP signing server)
npx @signet-auth/mcp-tools
Quick Start
Claude Code Plugin
Auto-sign every tool call in Claude Code with zero configuration:
# Option A: From the official Anthropic plugin marketplace
/plugin install signet@claude-plugins-official
# Option B: Add Signet as a marketplace source, then install
/plugin marketplace add Prismer-AI/signet
/plugin install signet@signet
Every tool call is signed with Ed25519 and logged to a hash-chained audit trail at ~/.signet/audit/.
Alternative install methods:
# From Git
claude plugin add --from https://github.com/Prismer-AI/signet
# Via signet CLI
signet claude install
Codex Plugin
Auto-sign every Bash tool call in Codex CLI:
git clone https://github.com/Prismer-AI/signet.git
cp -r signet/plugins/codex ~/.codex/plugins/signet
Then add the hook to ~/.codex/hooks.json:
{
"hooks": {
"PostToolUse": [{
"matcher": "Bash",
"hooks": [{
"type": "command",
"command": "node \"$HOME/.codex/plugins/signet/bin/sign.cjs\"",
"timeout": 5
}]
}]
}
}
Or use the MCP server for on-demand signing tools:
codex mcp add signet -- npx @signet-auth/mcp-tools
CLI
# Generate an agent identity
signet identity generate --name my-agent
# Sign an action
signet sign --key my-agent --tool "github_create_issue" \
--params '{"title":"fix bug"}' --target mcp://github.local
# Verify a receipt
signet verify receipt.json --pubkey my-agent
# Audit recent actions
signet audit --since 24h
# Verify log integrity
signet verify --chain
MCP Client Integration (TypeScript)
import { Client } from "@modelcontextprotocol/sdk/client/index.js";
import { StdioClientTransport } from "@modelcontextprotocol/sdk/client/stdio.js";
import { generateKeypair } from "@signet-auth/core";
import { SigningTransport } from "@signet-auth/mcp";
// Generate an agent identity
const { secretKey } = generateKeypair();
// Wrap any MCP transport -- all tool calls are now signed
const inner = new StdioClientTransport({ command: "my-mcp-server" });
const transport = new SigningTransport(inner, secretKey, "my-agent");
const client = new Client({ name: "my-agent", version: "1.0" }, {});
await client.connect(transport);
// Every callTool() is now cryptographically signed
const result = await client.callTool({
name: "echo",
arguments: { message: "Hello!" },
});
Every tools/call request gets a signed receipt injected into params._meta._signet.
MCP Server Verification
If you control the MCP server too, verify requests before execution:
import { FileNonceCache, verifyRequest } from "@signet-auth/mcp-server";
const nonceCache = new FileNonceCache(".signet/nonces.json");
server.setRequestHandler(CallToolRequestSchema, async (request) => {
const verified = verifyRequest(request, {
trustedKeys: ["ed25519:..."],
maxAge: 300,
nonceCache,
});
if (!verified.ok) return { content: [{ type: "text", text: verified.error }], isError: true };
if (!verified.trusted) return { content: [{ type: "text", text: "untrusted signer" }], isError: true };
console.log(`Verified: ${verified.signerName}`);
// process tool call...
});
Vercel AI SDK Integration
import { generateText } from "ai";
import { openai } from "@ai-sdk/openai";
import { generateKeypair } from "@signet-auth/core";
import { createSignetCallbacks } from "@signet-auth/vercel-ai";
const { secretKey } = generateKeypair();
const callbacks = createSignetCallbacks(secretKey, "my-agent");
const result = await generateText({
model: openai("gpt-4o"),
tools: { myTool },
...callbacks,
prompt: "...",
});
// Every tool call is now signed
console.log(callbacks.receipts);
Reference MCP Server
This repo also includes a minimal MCP reference server that demonstrates server-side verification with @signet-auth/mcp-server.
cd examples/mcp-agent
npm ci
npm run verifier-server
Available tools:
inspect_current_request— verifies the current MCP tool call if it includesparams._meta._signetverify_receipt— verifies a raw Signet receipt against a public keyverify_request_payload— verifies a synthetic MCPtools/callpayload offline
Environment variables:
SIGNET_TRUSTED_KEYS— comma-separateded25519:<base64>public keysSIGNET_REQUIRE_SIGNATURE—trueorfalse(defaulttrue)SIGNET_REQUIRE_TRUSTED_SIGNER—trueorfalse(defaulttrue)SIGNET_MAX_AGE— max receipt age in seconds (default300)SIGNET_EXPECTED_TARGET— optional expectedreceipt.action.target
Standalone MCP Signing Server
@signet-auth/mcp-tools exposes Signet signing, verification, and content hashing as MCP tools — plug into any MCP-compatible client:
npx @signet-auth/mcp-tools
Available tools: signet_generate_keypair, signet_sign, signet_verify, signet_content_hash.
Python SDK (LangChain / CrewAI / AutoGen + 6 more)
pip install signet-auth
from signet_auth import SigningAgent
# Create an agent identity (saved to ~/.signet/keys/)
agent = SigningAgent.create("my-agent", owner="willamhou")
# Sign any tool call -- receipt is auto-appended to audit log
receipt = agent.sign("github_create_issue", params={"title": "fix bug"})
# Verify
assert agent.verify(receipt)
# Query audit log
for record in agent.audit_query(since="24h"):
print(f"{record.receipt.ts} {record.receipt.action.tool}")
For plain Python tools, the lowest-friction entry point is the decorator layer:
from signet_auth import SigningAgent, signet_tool
agent = SigningAgent.create("tool-bot", owner="team")
@signet_tool(agent=agent, target="mcp://github.prod", audit_encrypt_params=True)
def create_issue(title: str, repo: str) -> str:
return f"{repo}:{title}"
If you run a Python MCP server or other execution boundary, use verify_request() with a durable nonce backend in the pilot shape:
from signet_auth import FileNonceChecker, VerifyOptions, verify_request
nonce_checker = FileNonceChecker(".signet/nonces.json")
opts = VerifyOptions(
trusted_keys=["ed25519:..."],
expected_target="mcp://github.prod",
nonce_checker=nonce_checker,
)
result = verify_request(request_params, opts)
if not result.ok:
raise ValueError(result.error or "verification failed")
if not result.trusted:
raise ValueError("untrusted signer")
LangChain Integration
from signet_auth import SigningAgent
from signet_auth.langchain import SignetCallbackHandler
agent = SigningAgent("my-agent")
handler = SignetCallbackHandler(agent)
# Every tool call is now signed + audited
chain.invoke(input, config={"callbacks": [handler]})
# Async chains supported too
from signet_auth.langchain import AsyncSignetCallbackHandler
CrewAI Integration
from signet_auth import SigningAgent
from signet_auth.crewai import install_hooks
agent = SigningAgent("my-agent")
install_hooks(agent)
# All CrewAI tool calls are now globally signed
crew.kickoff()
AutoGen Integration
from signet_auth import SigningAgent
from signet_auth.autogen import signed_tool, sign_tools
agent = SigningAgent("my-agent")
# Wrap a single tool
wrapped = signed_tool(tool, agent)
# Or wrap all tools at once
wrapped_tools = sign_tools([tool1, tool2], agent)
LangGraph Integration
LangGraph uses LangChain's callback system — the same handler works directly:
from signet_auth import SigningAgent
from signet_auth.langgraph import SignetCallbackHandler
agent = SigningAgent("my-agent")
handler = SignetCallbackHandler(agent)
result = graph.invoke(input, config={"callbacks": [handler]})
LlamaIndex Integration
from signet_auth import SigningAgent
from signet_auth.llamaindex import install_handler
agent = SigningAgent("my-agent")
handler = install_handler(agent)
# All tool call events are now signed
index = ... # your LlamaIndex setup
response = index.as_query_engine().query("What is Signet?")
# Access receipts
print(handler.receipts)
Pydantic AI Integration
from signet_auth import SigningAgent
from signet_auth.pydantic_ai_integration import SignetMiddleware
agent = SigningAgent("my-agent")
middleware = SignetMiddleware(agent)
@middleware.wrap
def my_tool(query: str) -> str:
return f"result: {query}"
Google ADK Integration
from signet_auth import SigningAgent
from signet_auth.google_adk import SignetPlugin
agent = SigningAgent("my-agent")
plugin = SignetPlugin(agent)
# Pass as callback to ADK agent
Smolagents Integration
from signet_auth import SigningAgent
from signet_auth.smolagents import signet_step_callback
agent = SigningAgent("my-agent")
callback = signet_step_callback(agent)
bot = CodeAgent(tools=[...], model=model, step_callbacks=[callback])
OpenAI Agents SDK Integration
from signet_auth import SigningAgent
from signet_auth.openai_agents import SignetAgentHooks
agent = SigningAgent("my-agent")
oai_agent = Agent(
name="assistant",
hooks=SignetAgentHooks(agent),
tools=[...],
)
Note: Tool call arguments are not yet available in the hook API (issue #939). Only the tool name is signed.
Low-Level API
from signet_auth import generate_keypair, sign, verify, Action
kp = generate_keypair()
action = Action("github_create_issue", params={"title": "fix bug"})
receipt = sign(kp.secret_key, action, "my-agent", "willamhou")
assert verify(receipt, kp.public_key)
Bilateral Receipt (Server Co-signing)
from signet_auth import generate_keypair, sign, sign_bilateral, verify_bilateral, Action
# Agent signs the tool call
agent_kp = generate_keypair()
action = Action("github_create_issue", params={"title": "fix bug"})
agent_receipt = sign(agent_kp.secret_key, action, "my-agent")
# Server co-signs with the response
server_kp = generate_keypair()
bilateral = sign_bilateral(
server_kp.secret_key, agent_receipt,
{"content": [{"type": "text", "text": "issue #42 created"}]},
"github-server",
)
assert verify_bilateral(bilateral, server_kp.public_key)
assert bilateral.v == 3 # v3 = bilateral receipt
How It Works
Your Agent
|
v
SigningTransport (wraps any MCP transport)
|
+---> Signs each tool call (Ed25519)
+---> Appends Action Receipt to local audit log (hash-chained)
+---> Forwards request to MCP server (unchanged)
Client-side signing works without changing the server. If you control the server too, add verifyRequest() and optional signResponse() for execution-boundary verification and bilateral receipts. signResponse() should only run after a successful trusted verifyRequest(), and it can now carry final executed / failed / rejected / requires_approval outcome state inside the bilateral signature.
Action Receipt
Every tool call starts with a signed receipt. Higher receipt versions add server co-signing (v3) and authorization chains (v4):
{
"v": 1,
"id": "rec_e7039e7e7714e84f...",
"action": {
"tool": "github_create_issue",
"params": {"title": "fix bug"},
"params_hash": "sha256:b878192252cb...",
"target": "mcp://github.local",
"transport": "stdio"
},
"signer": {
"pubkey": "ed25519:0CRkURt/tc6r...",
"name": "demo-bot",
"owner": "willamhou"
},
"ts": "2026-03-29T23:24:03.309Z",
"nonce": "rnd_dcd4e135799393...",
"sig": "ed25519:6KUohbnSmehP..."
}
The signature covers the entire receipt body (action + signer + timestamp + nonce) using RFC 8785 (JCS) canonical JSON. Modifying any field invalidates the signature.
CLI Commands
| Command | Description |
|---|---|
signet identity generate --name <n> | Generate Ed25519 identity (encrypted by default) |
signet identity generate --unencrypted | Generate without encryption (for CI) |
signet identity list | List all identities |
signet identity export --name <n> | Export public key as JSON |
signet sign --key <n> --tool <t> --params <json> --target <uri> | Sign an action |
signet sign --hash-only | Store only params hash (not raw params) |
signet sign --output <file> | Write receipt to file instead of stdout |
signet sign --no-log | Skip audit log append |
signet sign --encrypt-params | Encrypt action.params in the audit log while keeping the receipt output unchanged |
signet sign --policy <path> | Enforce policy before signing and embed PolicyAttestation |
signet verify <receipt.json> --pubkey <name> | Verify a receipt signature |
signet verify --chain | Verify audit log hash chain integrity |
signet audit | List recent actions |
signet audit --since <duration> | Filter by time (e.g. 24h, 7d) |
signet audit --tool <substring> | Filter by tool name |
signet audit --verify | Verify all receipt signatures |
signet audit --export <file> | Export records as JSON |
signet audit --bundle <dir> | Build a portable signed evidence bundle (records.jsonl + manifest.json + hash-summary.txt) for off-host audit handoff |
signet audit --bundle <dir> --include-trust-bundle <path> | Embed a trust bundle snapshot in the evidence package |
signet audit --restore <dir> | Re-verify a previously produced evidence bundle (works on any machine, no signet keystore required) |
signet audit --export <file> --decrypt-params | Export original audit records plus materialized_receipt with decrypted params |
signet explore | Browse receipts interactively (table, detail, stats, chain check) |
signet explore --show N | Inspect receipt #N with signature, policy, and chain info |
signet explore --show N --decrypt-params | Materialize encrypted action.params for local inspection |
signet explore --stats | Receipt statistics by tool, signer, and version |
signet delegate create ... --ttl 24h | Create a scoped delegation token (short-lived) |
signet delegate sign ... --chain <file> | Sign with delegation proof and produce a v4 receipt |
signet delegate verify-auth <receipt> --trusted-roots <name> | Verify authorization chain, scope, and trusted root |
signet policy validate <path> | Validate policy syntax and print its hash |
signet policy check <path> --tool <t> --params <json> | Dry-run whether an action would be allowed |
signet proxy --target <cmd> --key <name> | Run as MCP stdio proxy — sign all tool calls transparently (ephemeral server key) |
signet proxy ... --server-key <name> | Use a persistent server signing identity (required for trust bundles to anchor a stable server pubkey across restarts) |
signet proxy ... --policy <path> | Proxy with policy enforcement before signing |
signet verify <bilateral.json> --trust-bundle <bundle> --nonce-store <path> | Verify v3 bilateral receipts with replay protection that survives process restarts |
signet claude install | Install Claude Code plugin (PostToolUse signing hook) |
signet claude uninstall | Remove Claude Code plugin |
signet dashboard | Open local audit dashboard in browser |
Passphrase via interactive prompt or SIGNET_PASSPHRASE env var for CI.
Audit Dashboard
Run signet dashboard to open a local web UI for your audit log — no account, no network, just your local receipts.
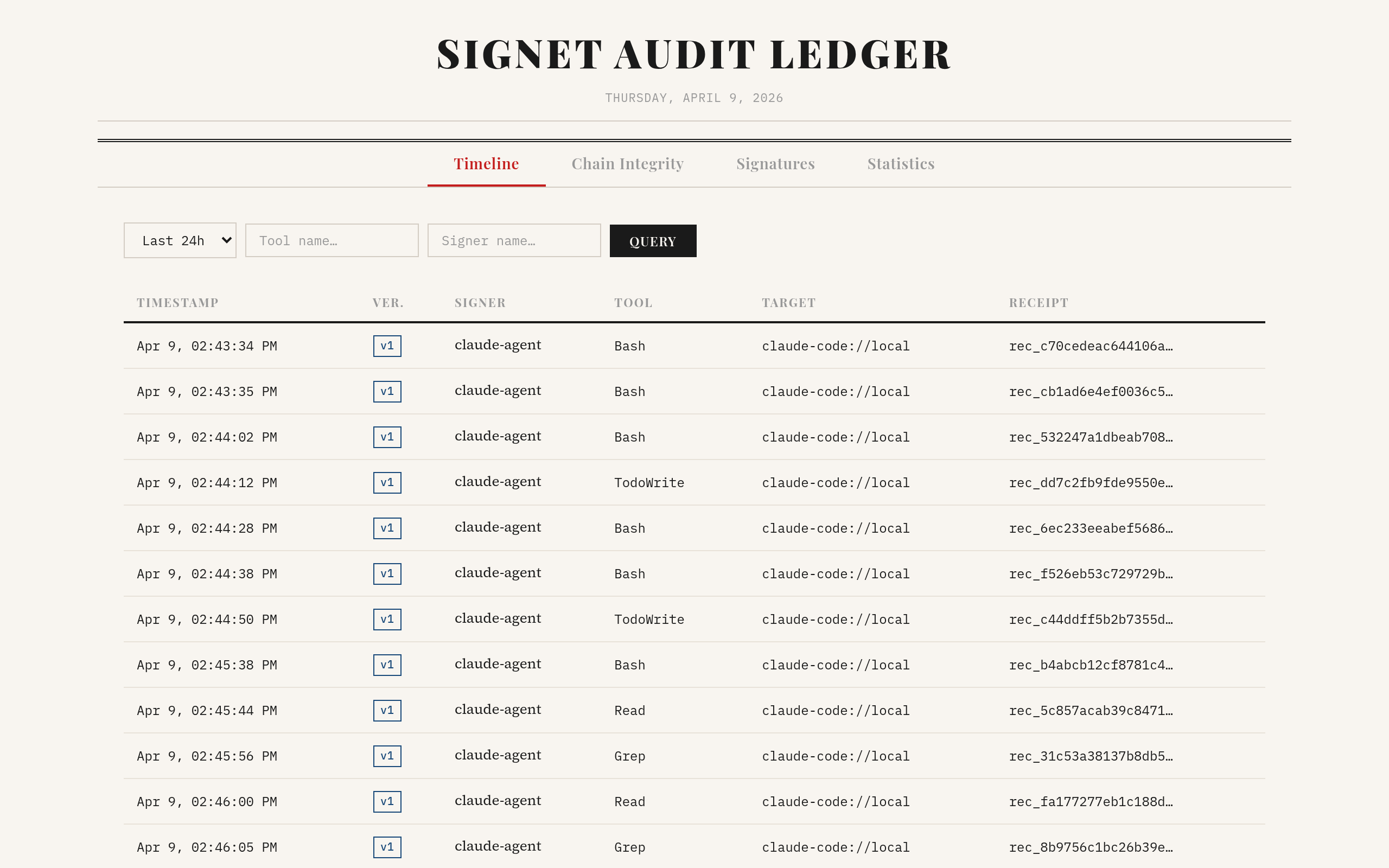
Timeline view: every tool call logged with signer, tool name, target, and receipt ID. Filter by time, tool, or signer.
The Chain Integrity tab verifies the SHA-256 hash chain across your entire audit log — any tampering or gap is pinpointed to the exact file and line:
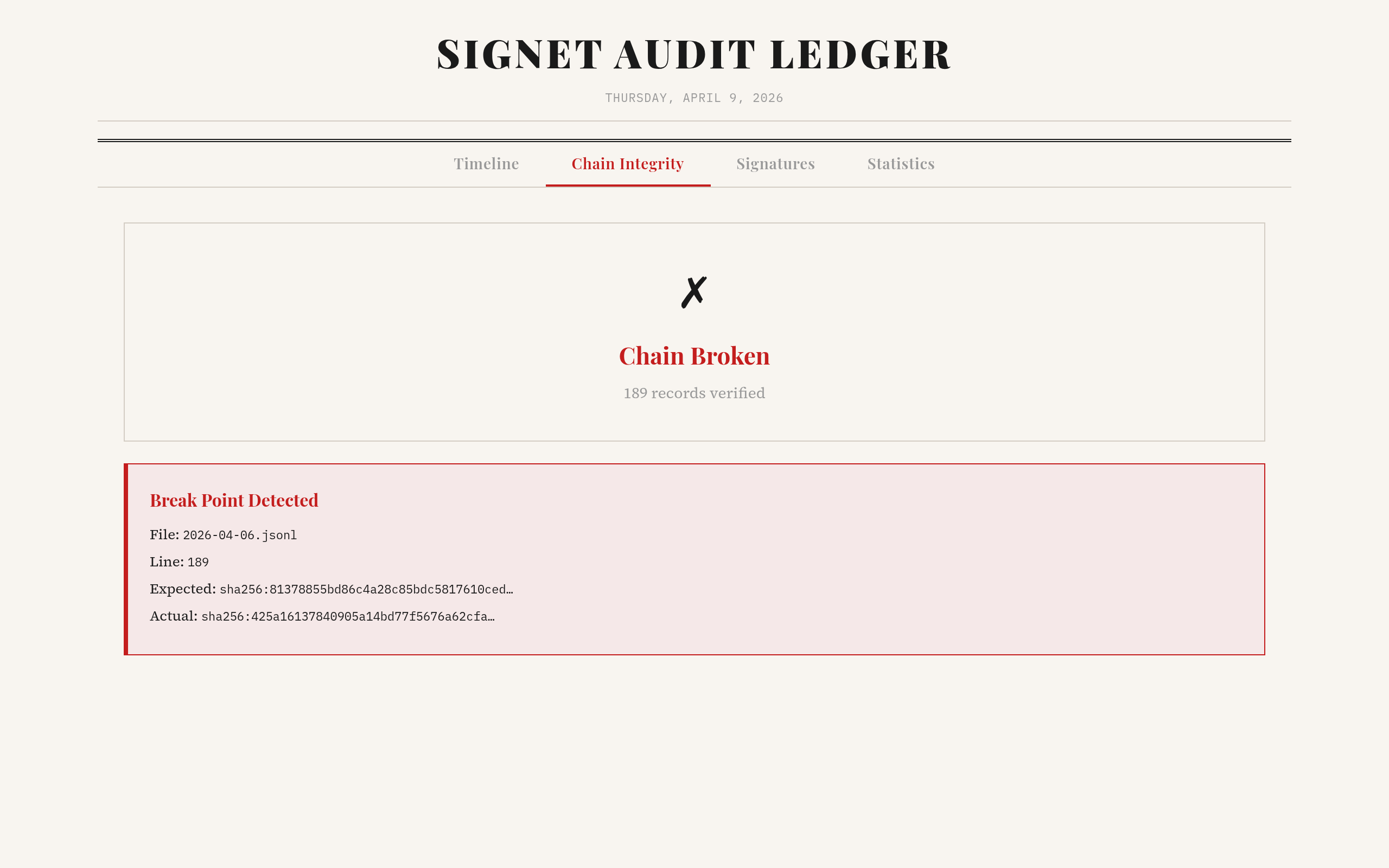
Chain broken at line 189: expected vs actual hash shown. This is what "append-only" actually looks like in practice.
Documentation
| Doc | Description |
|---|---|
| Architecture | System design, component overview, data flow |
| Security | Crypto primitives, threat model, key storage |
| Pilot Deployment Runbook | End-to-end runbook for a founder-assisted pilot: identities, trust bundle, proxy --server-key, durable replay, evidence bundles, outcome capture, on-compromise procedures |
| MCP Integration Guide | Step-by-step MCP setup with SigningTransport |
| CI/CD Integration | GitHub Actions example, key management for CI |
| Audit Log Guide | Querying, filtering, hash chain verification |
| Contributing | Build instructions, development workflow |
| Changelog | Version history |
Project Structure
signet/
├── crates/signet-core/ Rust core: identity, sign, verify, audit, keystore
├── signet-cli/ CLI tool (signet binary)
├── bindings/
│ ├── signet-ts/ WASM binding (wasm-bindgen)
│ └── signet-py/ Python binding (PyO3 + maturin)
├── plugins/
│ ├── claude-code/ Claude Code plugin (WASM signing + audit)
│ └── codex/ Codex CLI plugin (WASM signing + audit)
├── packages/
│ ├── signet-core/ @signet-auth/core — TypeScript wrapper
│ ├── signet-mcp/ @signet-auth/mcp — MCP SigningTransport middleware
│ ├── signet-mcp-server/ @signet-auth/mcp-server — Server verification
│ ├── signet-mcp-tools/ @signet-auth/mcp-tools — Standalone MCP signing server
│ ├── signet-node/ @signet-auth/node — Node local audit/operator helpers
│ └── signet-vercel-ai/ @signet-auth/vercel-ai — Vercel AI SDK middleware
├── examples/
│ ├── wasm-roundtrip/ WASM validation tests
│ └── mcp-agent/ MCP agent, echo server, and verifier server example
├── docs/ Design docs, specs, plans
├── LICENSE-APACHE
└── LICENSE-MIT
Building from Source
Prerequisites
- Rust (1.70+)
- wasm-pack
- Node.js (18+)
- Python (3.10+) + maturin (for Python binding)
Build
# Rust core + CLI
cargo build --release -p signet-cli
# WASM binding
wasm-pack build bindings/signet-ts --target nodejs --out-dir ../../packages/signet-core/wasm
# TypeScript packages
cd packages/signet-core && npm run build
cd packages/signet-mcp && npm run build
cd packages/signet-mcp-server && npm run build
cd packages/signet-mcp-tools && npm run build
cd packages/signet-node && npm run build
cd packages/signet-vercel-ai && npm run build
# Python binding
cd bindings/signet-py
pip install maturin
maturin develop
Test
# Rust tests
cargo test --workspace
# Python tests
cd bindings/signet-py && pytest tests/ -v
# WASM roundtrip
node examples/wasm-roundtrip/test.mjs
# TypeScript tests
cd packages/signet-core && npm test
cd packages/signet-mcp && npm test
cd packages/signet-mcp-server && npm test
cd packages/signet-mcp-tools && npm test
cd packages/signet-node && npm test
# Plugin tests
cd plugins/claude-code && npm test
cd plugins/codex && npm test
# Vercel AI SDK tests
cd packages/signet-vercel-ai && npm test
# Reference verifier server smoke test
cd examples/mcp-agent && npm run smoke
Security
- Ed25519 signatures (128-bit security level,
ed25519-dalek) - Argon2id key derivation (OWASP recommended minimum)
- XChaCha20-Poly1305 key encryption with authenticated associated data (AAD)
- SHA-256 hash chain for tamper-evident audit log
- RFC 8785 (JCS) canonical JSON for deterministic signatures
Keys stored at ~/.signet/keys/ with 0600 permissions. Override with SIGNET_HOME env var.
What Signet proves
- Agent key X signed intent to call tool Y with params Z at time T
What Signet does NOT prove (yet)
- That the MCP server executed the action (use bilateral receipts with
signResponse()for server co-signing — shipped in v0.4) - That signer.owner actually controls the key (planned: identity registry)
Signet is first an evidence layer: it proves what happened. It can also enforce checks at the signing boundary and execution boundary, but it does not replace sandboxing, least-privilege design, or human approval where those are required.
Related Projects
- Prismer Cloud — Full agent harness with evolution engine, memory layer, community, and built-in Ed25519/DID identity. Use Prismer Cloud for the complete agent platform; use Signet when you only need the standalone attestation layer.
- Prismer.AI — The open-source AI research platform
Star History
If Signet is useful to you, please star this repo — it helps more teams find it.
License
Apache-2.0 + MIT dual license.