MySQL MCP Server
Provides read-only access to MySQL databases, allowing LLMs to inspect schemas and execute queries.
@davewind/mysql-mcp-server
A Model Context Protocol server that provides read-only access to Mysql databases. This server enables LLMs to inspect database schemas and execute read-only queries.
Key Features
1.Read-Only Database Access: Enforces read-only operations through SQL validation and READ ONLY transactions
2.Schema Discovery: Automatically identifies and exposes database table structures
3.SQL Query Execution: Provides a query tool that accepts and executes SELECT statements
4.Model Context Protocol Compliance: Implements the MCP specification for seamless integration with compatible LLMs
5.Simple Configuration: Easy setup with minimal configuration required
Tools
- query
- Execute read-only SQL queries against the connected database
- Input:
sql(string): The SQL query to execute - All queries are executed within a READ ONLY transaction
Resources
The server provides schema information for each table in the database:
- Table Schemas (
mysql://user:password@localhost:3306/database)- JSON schema information for each table
- Includes column names and data types
- Automatically discovered from database metadata
Install
npm install @davewind/mysql-mcp-server -g
Configuration
MCP settings configuration file:
recommended use
{
"mcpServers": {
"mysql": {
"command": "npx",
"args": ["-y", "@davewind/mysql-mcp-server", "mysql://user:password@localhost:port/database"],
}
}
}
Test
Replace mysql://user:password@localhost:port/ and npm run inspector
"scripts": {
"inspector": "npx @modelcontextprotocol/[email protected] build/index.js mysql://user:password@localhost:port/database
}
Env
node v18 +
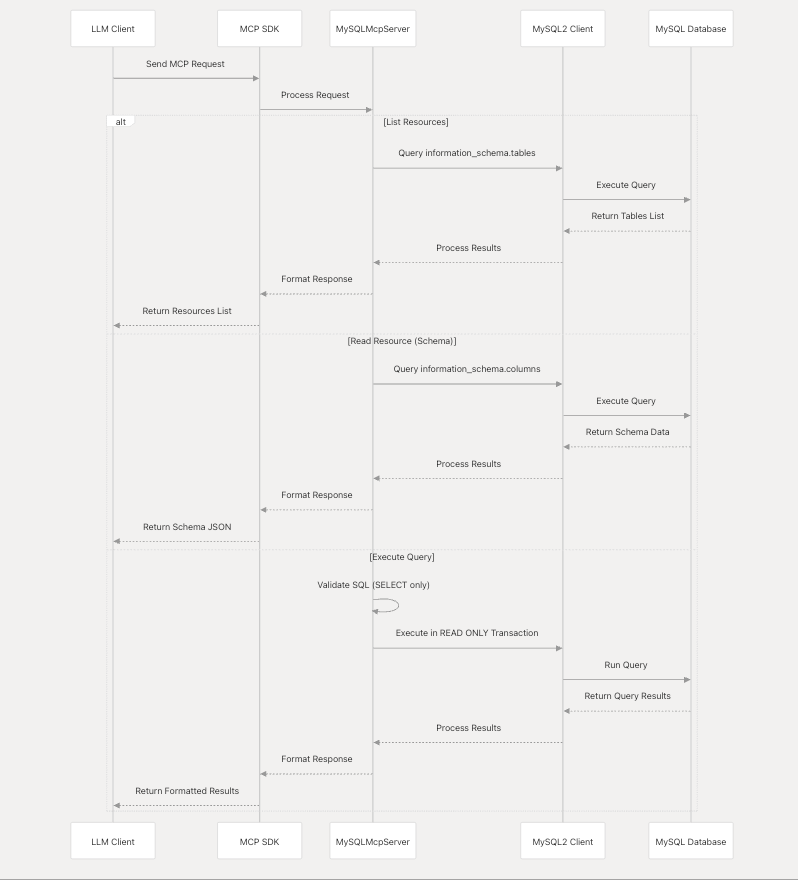
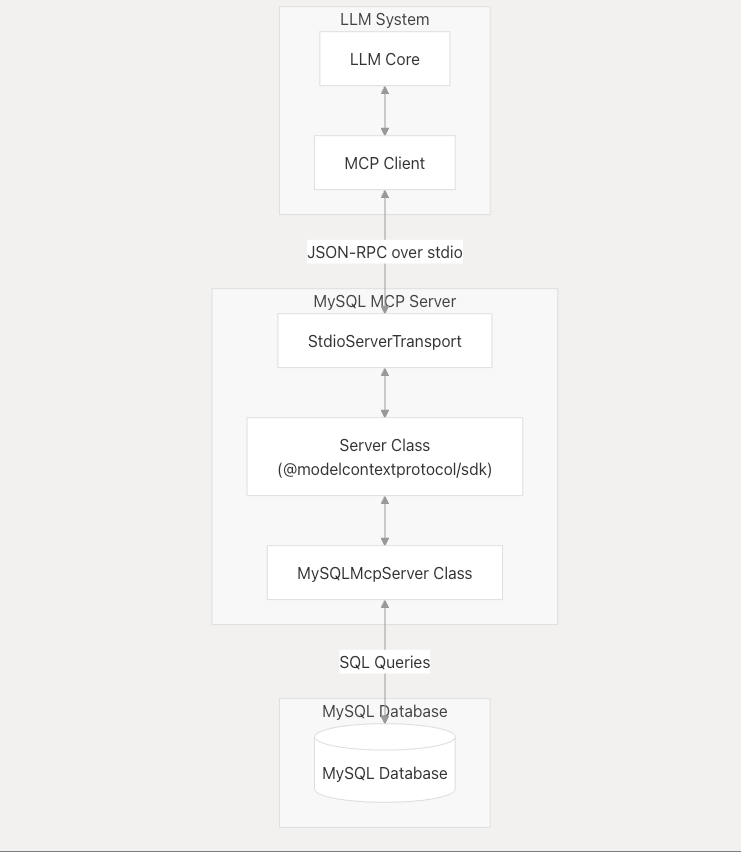
System Architecture
The MySQL MCP Server acts as an intermediary between LLMs and MySQL databases, processing requests according to the Model Context Protocol.
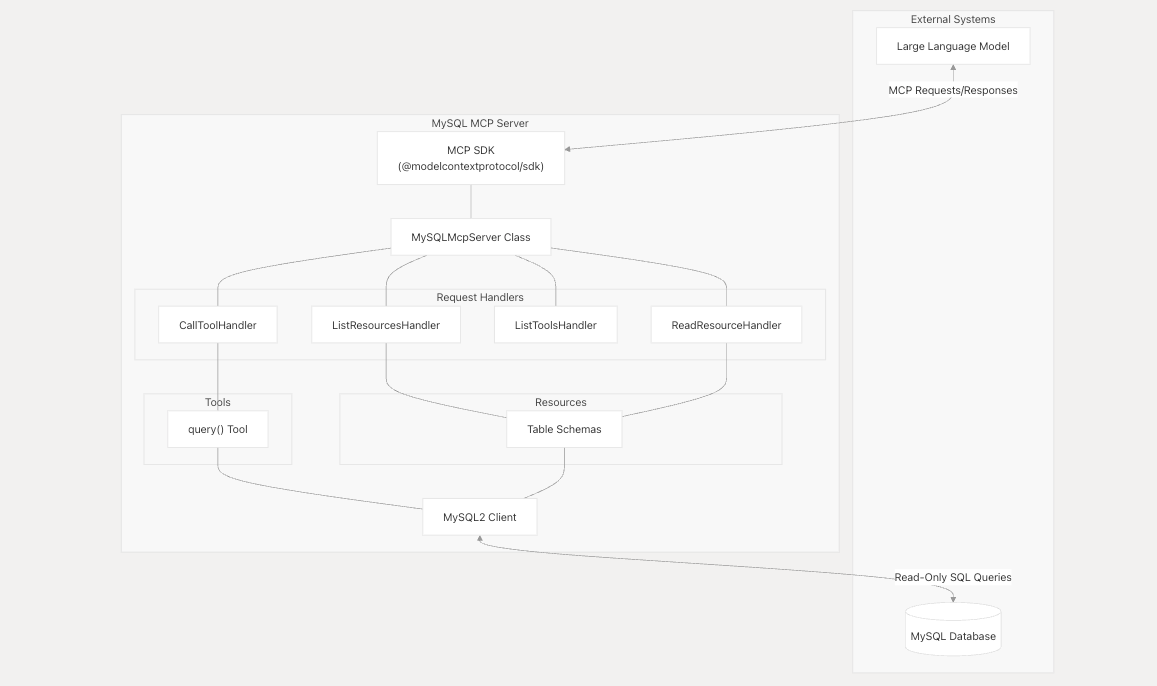
Component Interaction
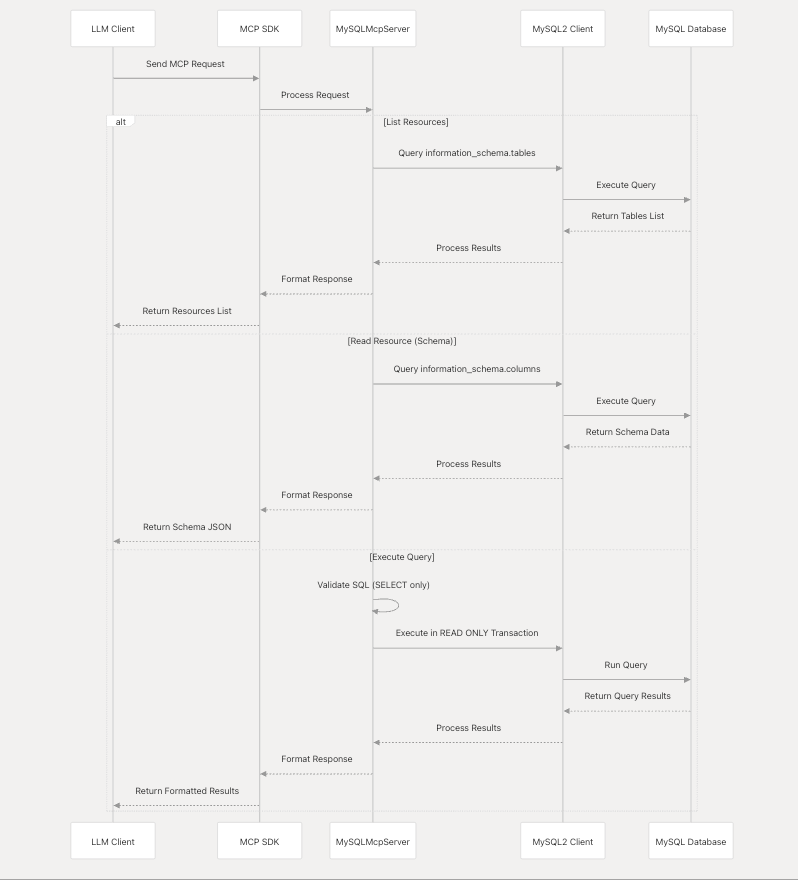
Component Interaction
Security Model
The MySQL MCP Server implements a strict security model to ensure that database access is read-only.
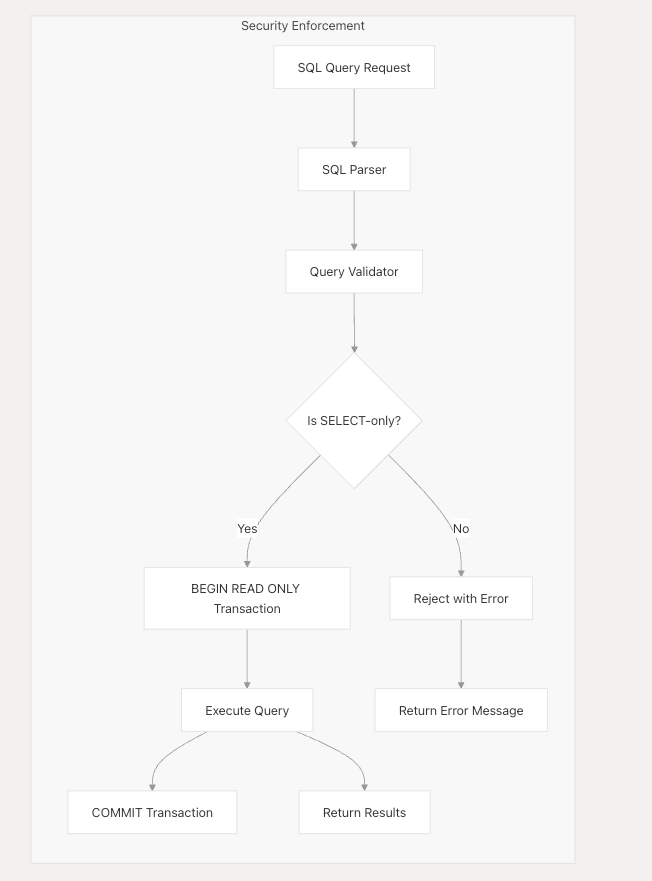
Security measures include:
1.SQL query validation to allow only SELECT statements 2.Execution of all queries within READ ONLY transactions 3.No support for data modification operations (INSERT, UPDATE, DELETE, etc.) 4. No support for database schema modification (CREATE, ALTER, DROP, etc.)
Integration with LLMs
The MySQL MCP Server is designed to work with any LLM system that supports the Model Context Protocol. It communicates through JSON-RPC over stdio, following the MCP specification.
License
MIT
관련 서버
MongoDB
A Model Context Protocol Server for MongoDB
ローカルNeo4jコンテナ
Manages personal knowledge using a local Neo4j container, with data imported from JSON files.
Unofficial Open Targets
Unofficial server for accessing Open Targets platform data for gene-drug-disease associations research.
Dremio
Integrate Large Language Models (LLMs) with the Dremio data lakehouse platform.
MCP for Neo4j
Connects to Neo4j graph databases with ability to use GDS functions ( when available), a read only mode , and set the sample size for schema detection
ORMCP
ORMCP provides a curated, object-oriented, MCP-compliant view of relational data in any JDBC-compliant database (e.g., PostgreSQL, MySQL, Oracle, SQL Server, DB2, SQLite) — improving reasoning clarity, reducing token usage, and establishing a clear governance boundary.
Octopus MCP Server
A high-performance, persistent knowledge base MCP server built with Rust. Supports local deployment with hybrid datastores like Qdrant, Neo4j, and Redis.
MongoDB Mongoose MCP
An MCP server for MongoDB with optional Mongoose schema support.
Quick Data for Windows MCP
A Windows-optimized server for performing data analytics on JSON and CSV files, designed for Claude Desktop integration.
Fedspeak MCP Server
Access and analyze Federal Reserve (FOMC) statements.