MySQL MCP Server
Provides read-only access to MySQL databases, allowing LLMs to inspect schemas and execute queries.
@davewind/mysql-mcp-server
A Model Context Protocol server that provides read-only access to Mysql databases. This server enables LLMs to inspect database schemas and execute read-only queries.
Key Features
1.Read-Only Database Access: Enforces read-only operations through SQL validation and READ ONLY transactions
2.Schema Discovery: Automatically identifies and exposes database table structures
3.SQL Query Execution: Provides a query tool that accepts and executes SELECT statements
4.Model Context Protocol Compliance: Implements the MCP specification for seamless integration with compatible LLMs
5.Simple Configuration: Easy setup with minimal configuration required
Tools
- query
- Execute read-only SQL queries against the connected database
- Input:
sql(string): The SQL query to execute - All queries are executed within a READ ONLY transaction
Resources
The server provides schema information for each table in the database:
- Table Schemas (
mysql://user:password@localhost:3306/database)- JSON schema information for each table
- Includes column names and data types
- Automatically discovered from database metadata
Install
npm install @davewind/mysql-mcp-server -g
Configuration
MCP settings configuration file:
recommended use
{
"mcpServers": {
"mysql": {
"command": "npx",
"args": ["-y", "@davewind/mysql-mcp-server", "mysql://user:password@localhost:port/database"],
}
}
}
Test
Replace mysql://user:password@localhost:port/ and npm run inspector
"scripts": {
"inspector": "npx @modelcontextprotocol/[email protected] build/index.js mysql://user:password@localhost:port/database
}
Env
node v18 +
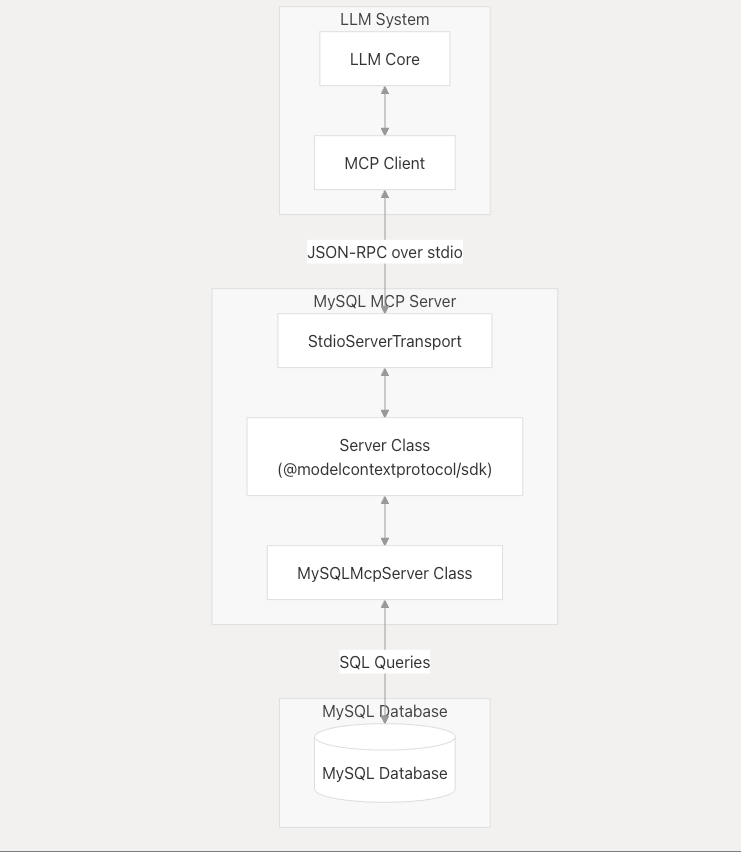
System Architecture
The MySQL MCP Server acts as an intermediary between LLMs and MySQL databases, processing requests according to the Model Context Protocol.
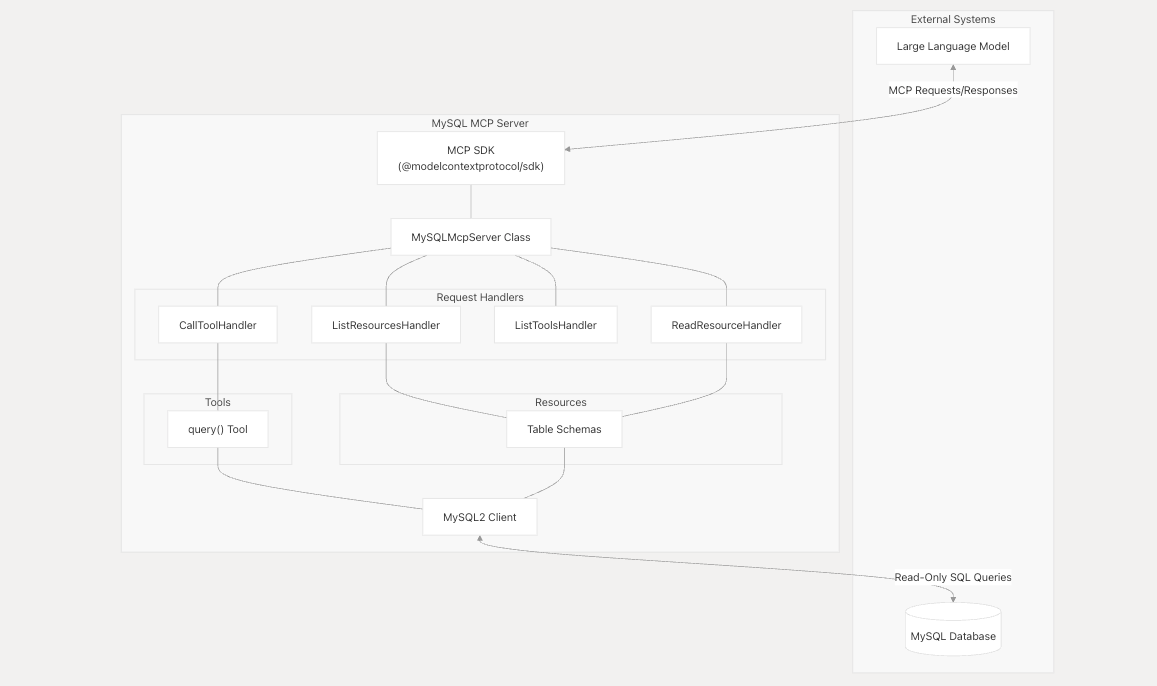
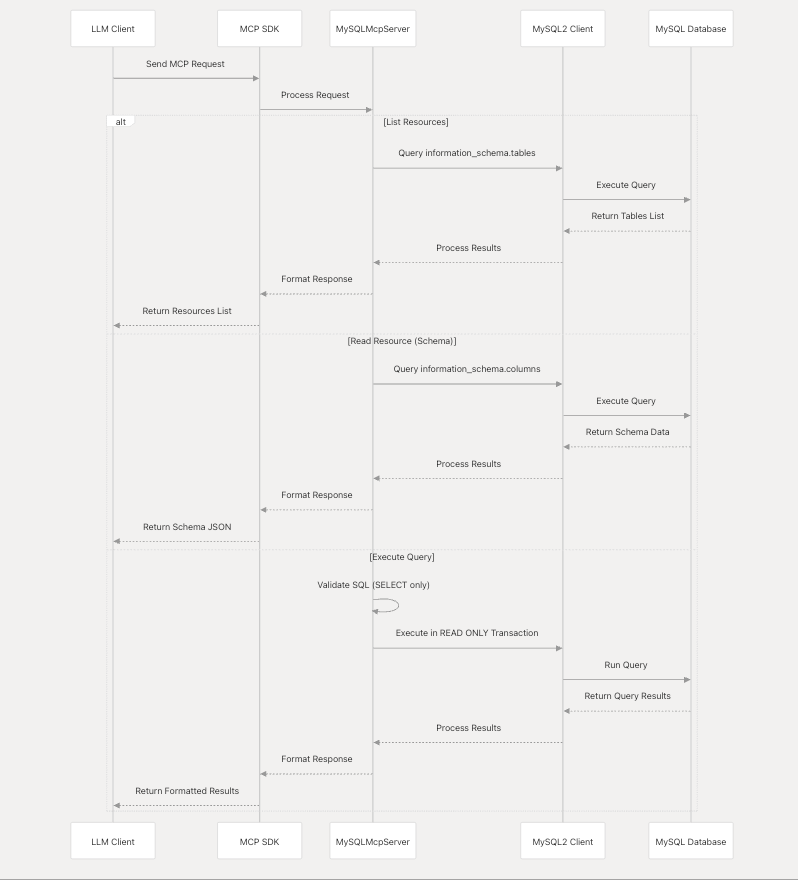
Component Interaction
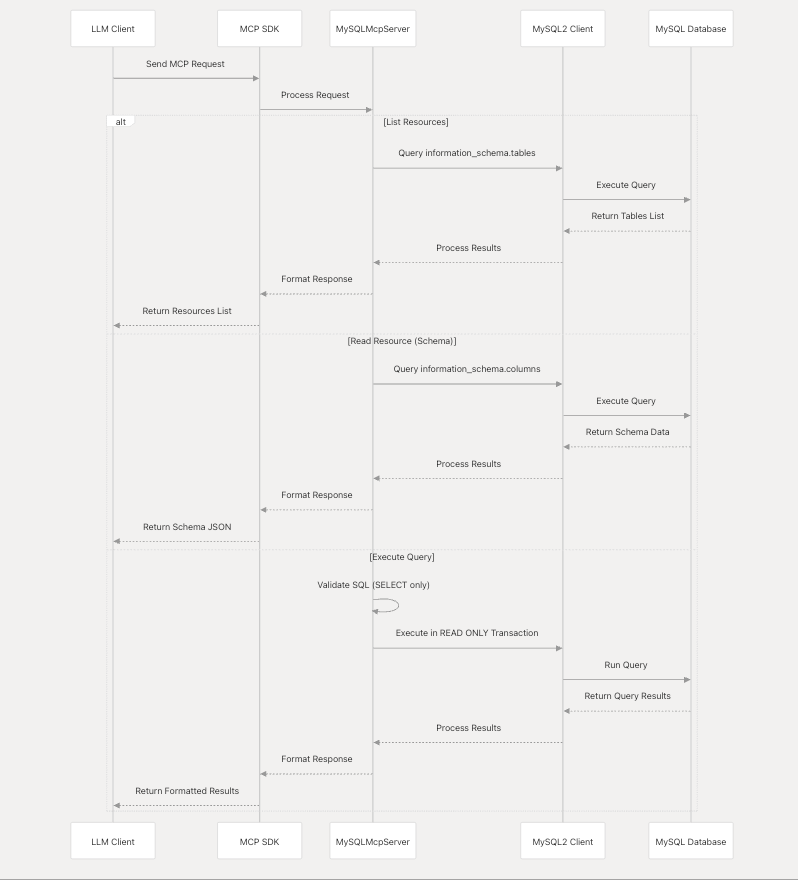
Component Interaction
Security Model
The MySQL MCP Server implements a strict security model to ensure that database access is read-only.
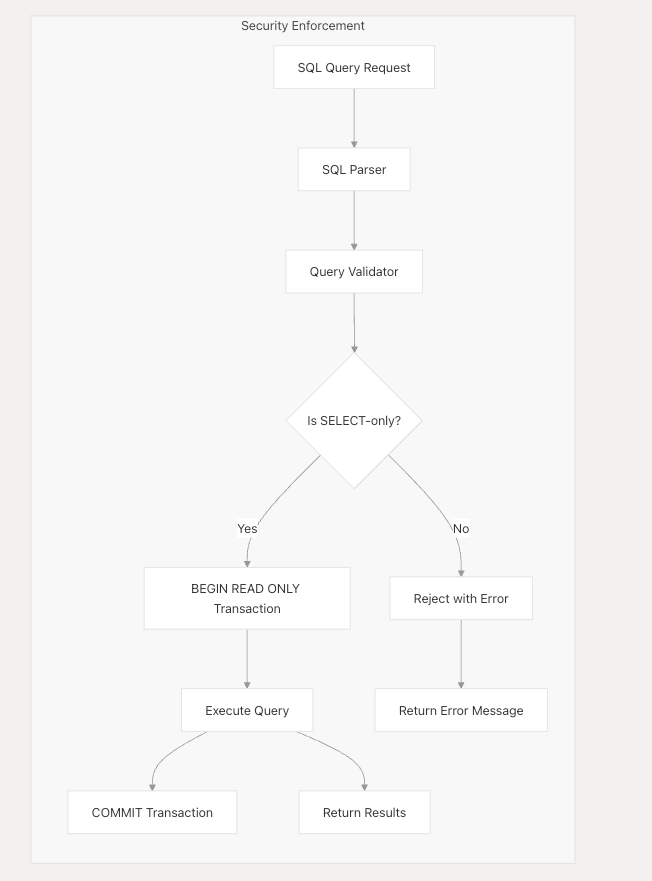
Security measures include:
1.SQL query validation to allow only SELECT statements 2.Execution of all queries within READ ONLY transactions 3.No support for data modification operations (INSERT, UPDATE, DELETE, etc.) 4. No support for database schema modification (CREATE, ALTER, DROP, etc.)
Integration with LLMs
The MySQL MCP Server is designed to work with any LLM system that supports the Model Context Protocol. It communicates through JSON-RPC over stdio, following the MCP specification.
License
MIT
Serveurs connexes
Apache Doris
MCP Server For Apache Doris, an MPP-based real-time data warehouse.
Poland KRS
Access to Polish National Court Register (KRS) — the government's authoritative registry of all businesses, foundations, and other legal entities.
Database Server
A Model Context Protocol (MCP) server that provides multi-database query execution capabilities with support for SQLite, PostgreSQL, and MySQL databases. Includes a built-in Web UI for managing database connections.
Sanity MCP Server
Connects Sanity projects with AI tools, allowing AI models to understand content structure and perform operations using natural language.
OpenAlex Author Disambiguation
Disambiguate authors and resolve institutions using the OpenAlex.org API.
engram-rs-mcp
MCP server for engram — persistent, brain-like memory for AI agents.
AudioAlpha
AudioAlpha turns 100+ daily finance and crypto podcasts into structured intelligence — α-sentiment scores, narrative signals, asset mentions, transcripts, and market snapshots with 40+ custom metrics. Built for AI-driven research and trading workflows.
SQL Server Express
An MCP server for interacting with Microsoft SQL Server Express databases.
Wormhole Metrics MCP
Analyzes cross-chain activity on the Wormhole protocol, providing insights into transaction volumes, top assets, and key performance indicators.
Kyomi MCP
Data intelligence platform - query your database in natural language, build dashboards, and set up automated alerts that monitor your metrics 24/7.