MySQL MCP Server
Provides read-only access to MySQL databases, allowing LLMs to inspect schemas and execute queries.
@davewind/mysql-mcp-server
A Model Context Protocol server that provides read-only access to Mysql databases. This server enables LLMs to inspect database schemas and execute read-only queries.
Key Features
1.Read-Only Database Access: Enforces read-only operations through SQL validation and READ ONLY transactions
2.Schema Discovery: Automatically identifies and exposes database table structures
3.SQL Query Execution: Provides a query tool that accepts and executes SELECT statements
4.Model Context Protocol Compliance: Implements the MCP specification for seamless integration with compatible LLMs
5.Simple Configuration: Easy setup with minimal configuration required
Tools
- query
- Execute read-only SQL queries against the connected database
- Input:
sql(string): The SQL query to execute - All queries are executed within a READ ONLY transaction
Resources
The server provides schema information for each table in the database:
- Table Schemas (
mysql://user:password@localhost:3306/database)- JSON schema information for each table
- Includes column names and data types
- Automatically discovered from database metadata
Install
npm install @davewind/mysql-mcp-server -g
Configuration
MCP settings configuration file:
recommended use
{
"mcpServers": {
"mysql": {
"command": "npx",
"args": ["-y", "@davewind/mysql-mcp-server", "mysql://user:password@localhost:port/database"],
}
}
}
Test
Replace mysql://user:password@localhost:port/ and npm run inspector
"scripts": {
"inspector": "npx @modelcontextprotocol/[email protected] build/index.js mysql://user:password@localhost:port/database
}
Env
node v18 +
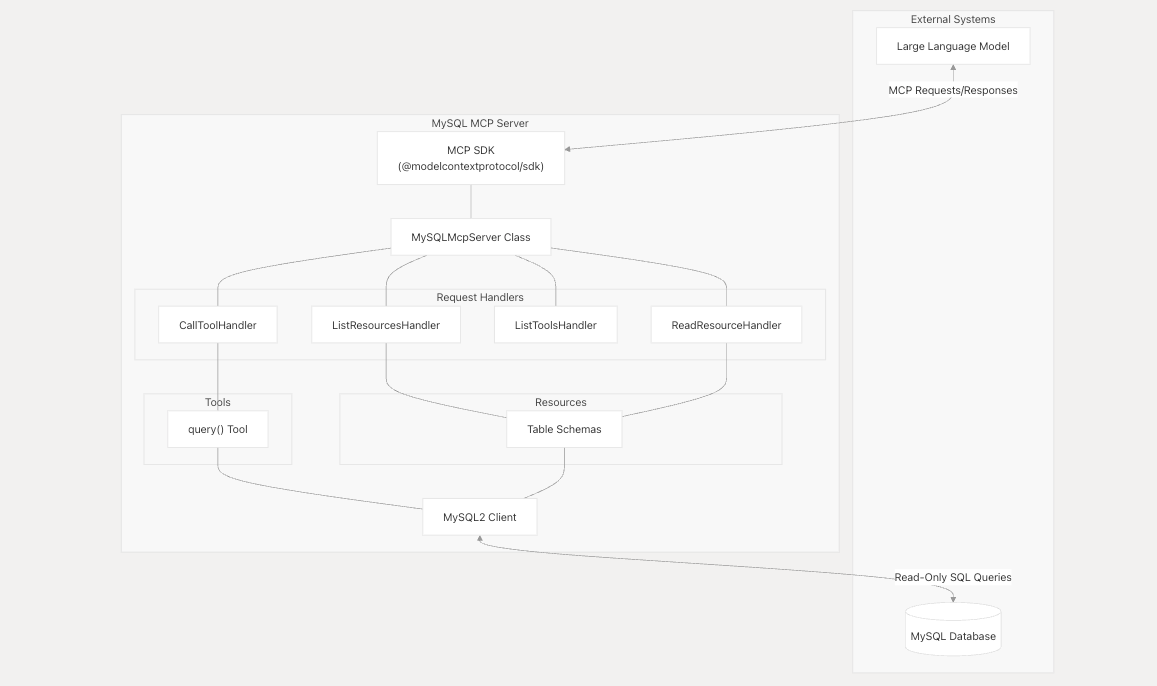
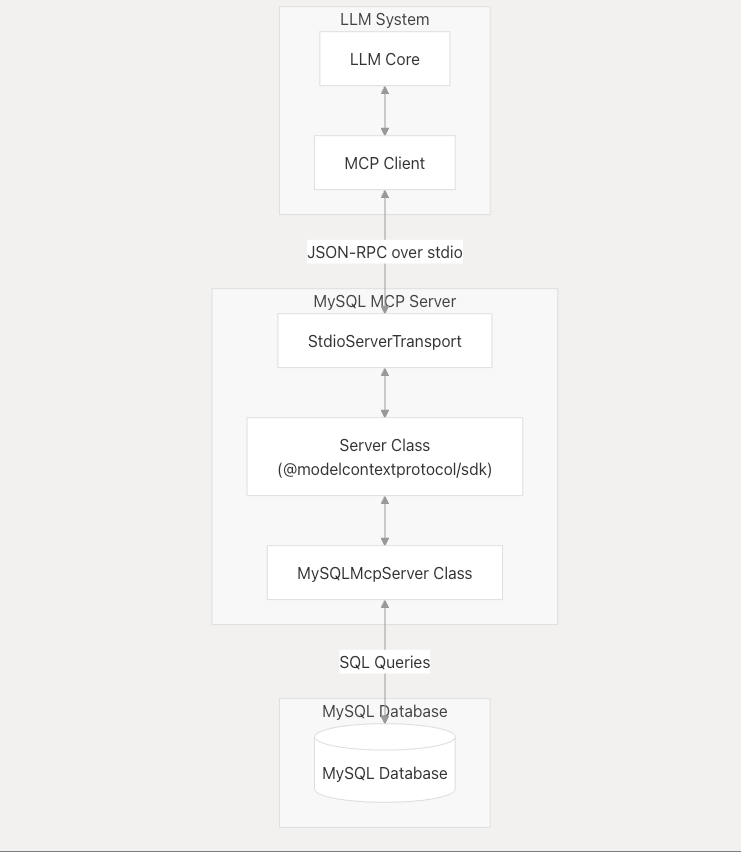
System Architecture
The MySQL MCP Server acts as an intermediary between LLMs and MySQL databases, processing requests according to the Model Context Protocol.
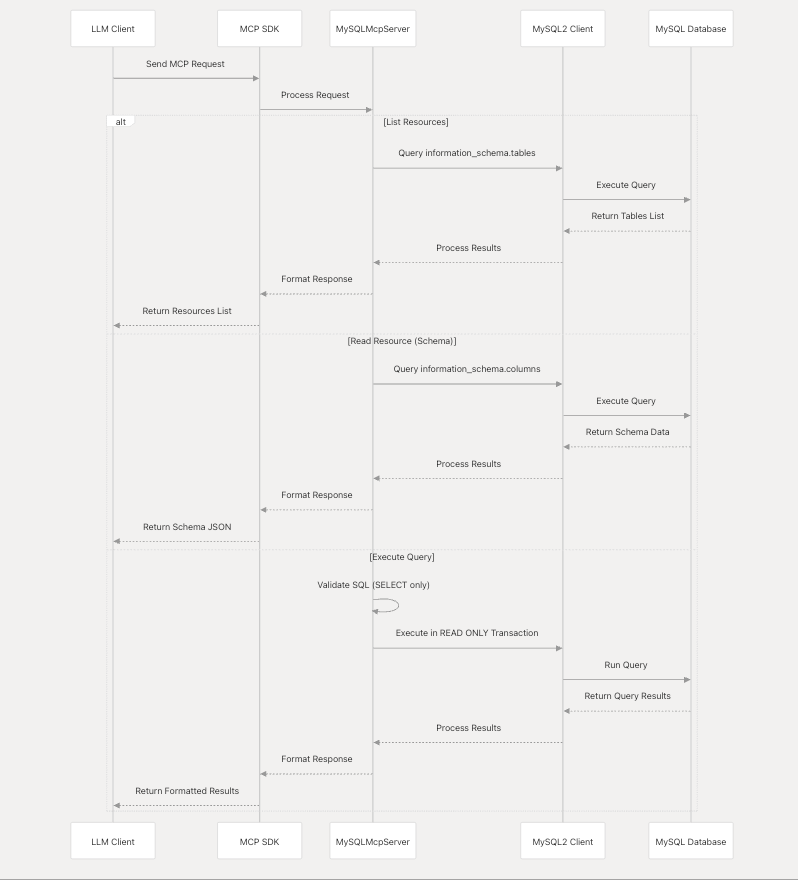
Component Interaction
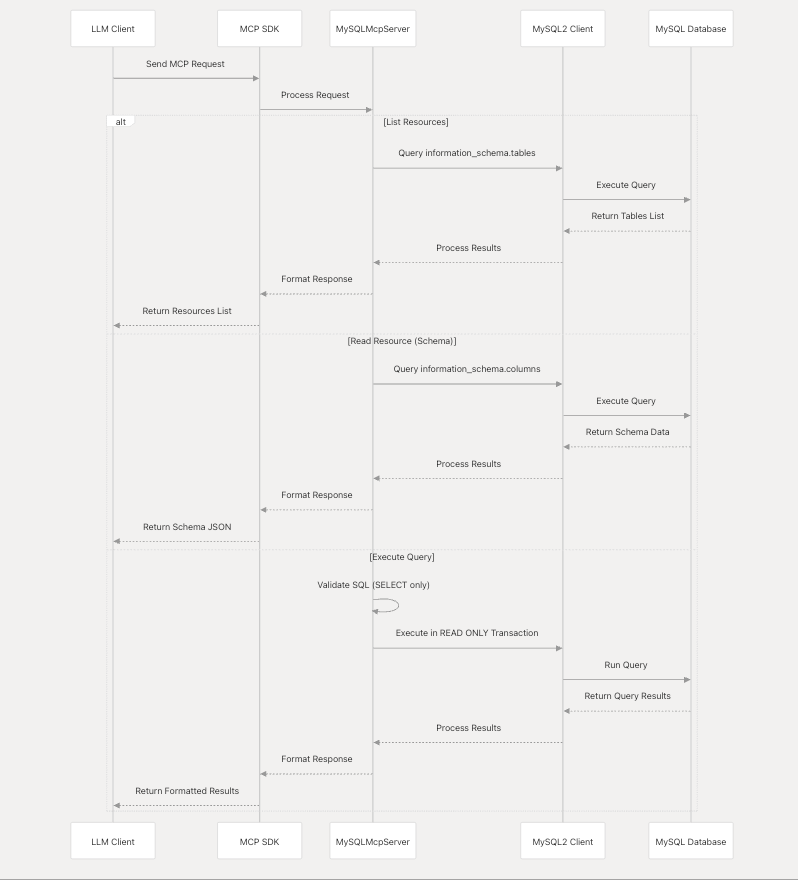
Component Interaction
Security Model
The MySQL MCP Server implements a strict security model to ensure that database access is read-only.
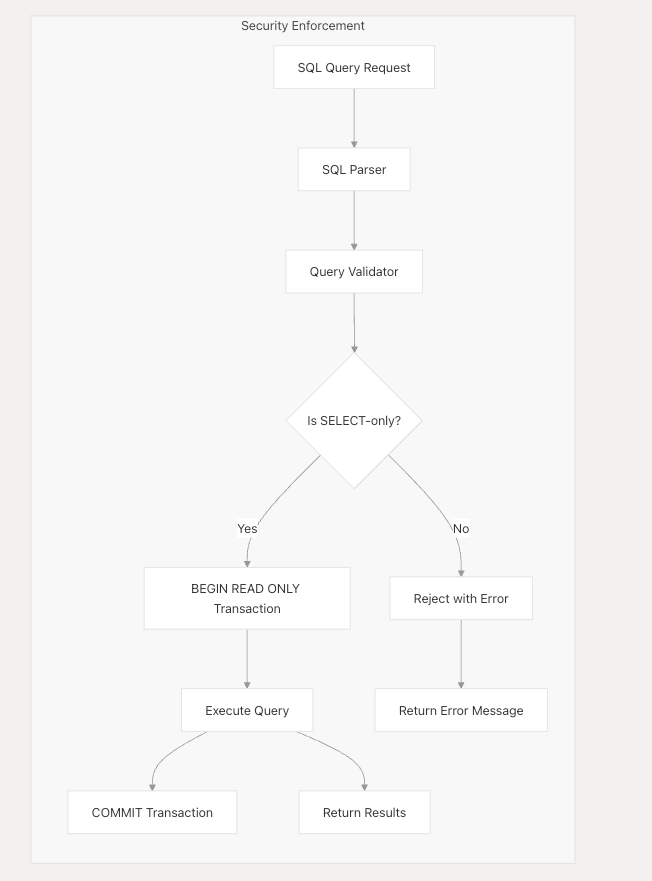
Security measures include:
1.SQL query validation to allow only SELECT statements 2.Execution of all queries within READ ONLY transactions 3.No support for data modification operations (INSERT, UPDATE, DELETE, etc.) 4. No support for database schema modification (CREATE, ALTER, DROP, etc.)
Integration with LLMs
The MySQL MCP Server is designed to work with any LLM system that supports the Model Context Protocol. It communicates through JSON-RPC over stdio, following the MCP specification.
License
MIT
相關伺服器
aml
AML Watcher MCP Server gives AI agents direct, real-time access to AML Watcher's proprietary sanctions, watchlist, and PEP databases. Connect your agentic workflows to 215+ sanctions regimes, 2.6M+ PEP profiles, and coverage across 235+ countries, no complex integrations required.
CData Excel Online
A read-only MCP server for querying live data from Excel Online using CData's JDBC driver.
MCP Neo4j Server
Integrate the Neo4j graph database with clients through natural language interactions.
CouchDB MCP Server
A server for interacting with CouchDB databases.
Outreach.io by CData
A read-only MCP server for querying live data from Outreach.io using the CData JDBC Driver.
AITable
Provides read and write access to AITable.ai, a collaborative database and spreadsheet platform.
MySQL MCP Server
Provides AI agents with direct access to query, search, and analyze MySQL databases.
MongoDB Atlas MCP Server
Manage MongoDB Atlas projects, including cluster creation, user management, and network access configuration.
Fedspeak MCP Server
Access and analyze Federal Reserve (FOMC) statements.
FalkorDB
Query and interact with FalkorDB graph databases using AI models.