Remote MCP Server on Cloudflare
A remote MCP server deployable on Cloudflare Workers with OAuth login support, using Cloudflare KV for data storage.
Remote MCP Server on Cloudflare
Let's get a remote MCP server up-and-running on Cloudflare Workers complete with OAuth login!
Develop locally
# clone the repository
git clone https://github.com/cloudflare/ai.git
# Or if using ssh:
# git clone [email protected]:cloudflare/ai.git
# install dependencies
cd ai
# Note: using pnpm instead of just "npm"
pnpm install
# run locally
npx nx dev remote-mcp-server
You should be able to open http://localhost:8787/ in your browser
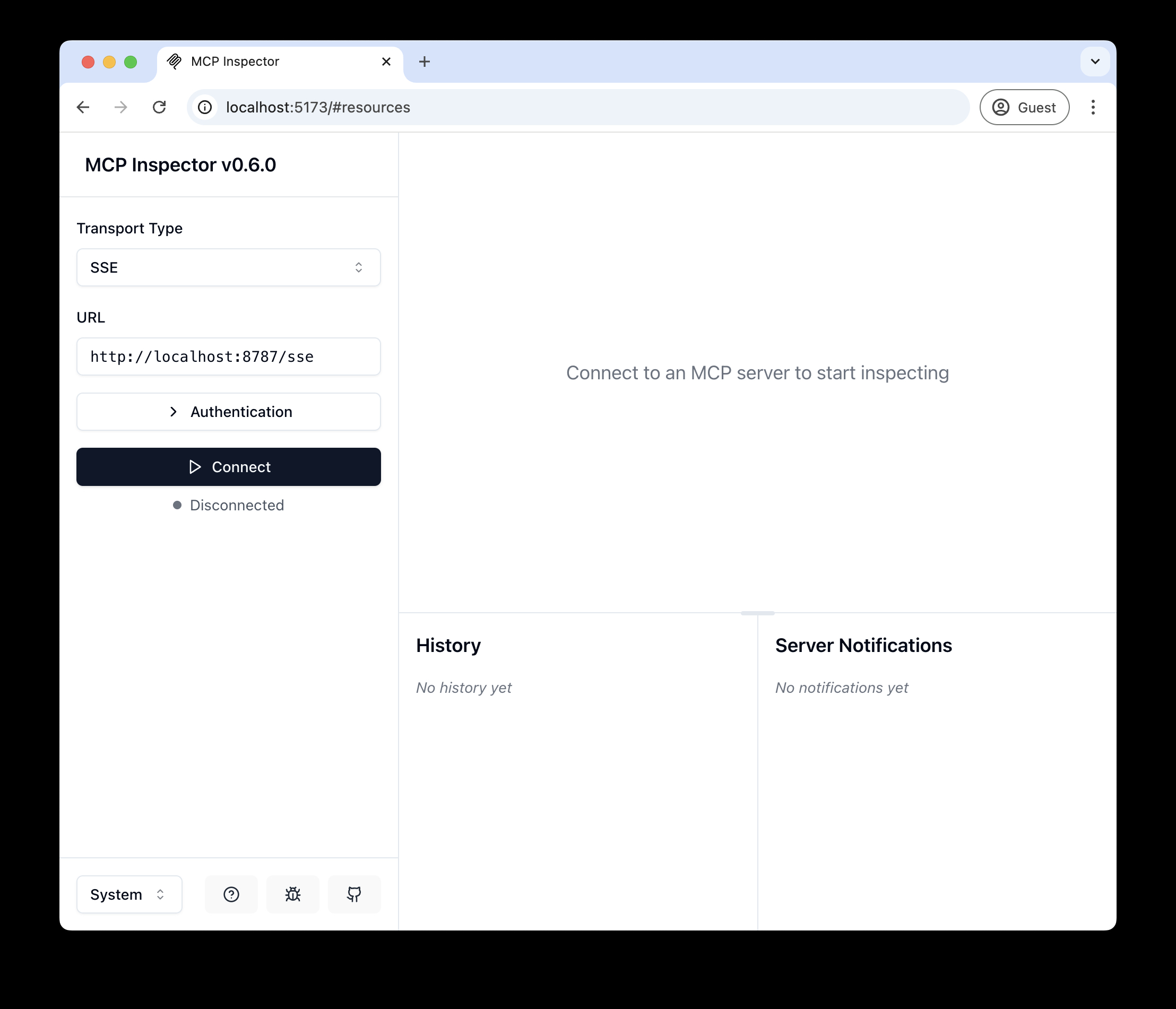
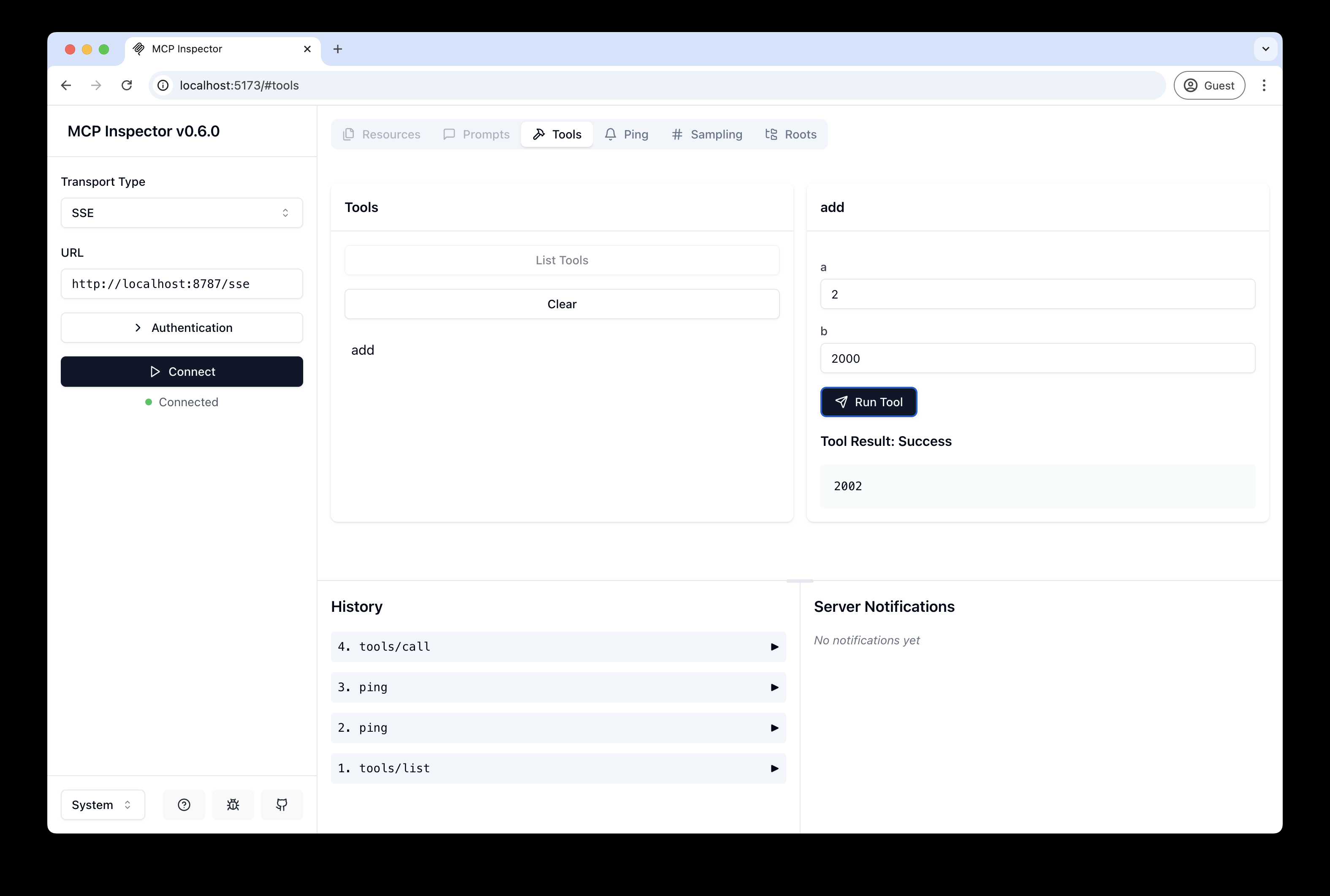
Connect the MCP inspector to your server
To explore your new MCP api, you can use the MCP Inspector.
- Start it with
npx @modelcontextprotocol/inspector - Within the inspector, switch the Transport Type to
SSEand enterhttp://localhost:8787/sseas the URL of the MCP server to connect to, and click "Connect" - You will navigate to a (mock) user/password login screen. Input any email and pass to login.
- You should be redirected back to the MCP Inspector and you can now list and call any defined tools!
Connect Claude Desktop to your local MCP server
The MCP inspector is great, but we really want to connect this to Claude! Follow Anthropic's Quickstart and within Claude Desktop go to Settings > Developer > Edit Config to find your configuration file.
Open the file in your text editor and replace it with this configuration:
{
"mcpServers": {
"math": {
"command": "npx",
"args": [
"mcp-remote",
"http://localhost:8787/sse"
]
}
}
}
This will run a local proxy and let Claude talk to your MCP server over HTTP
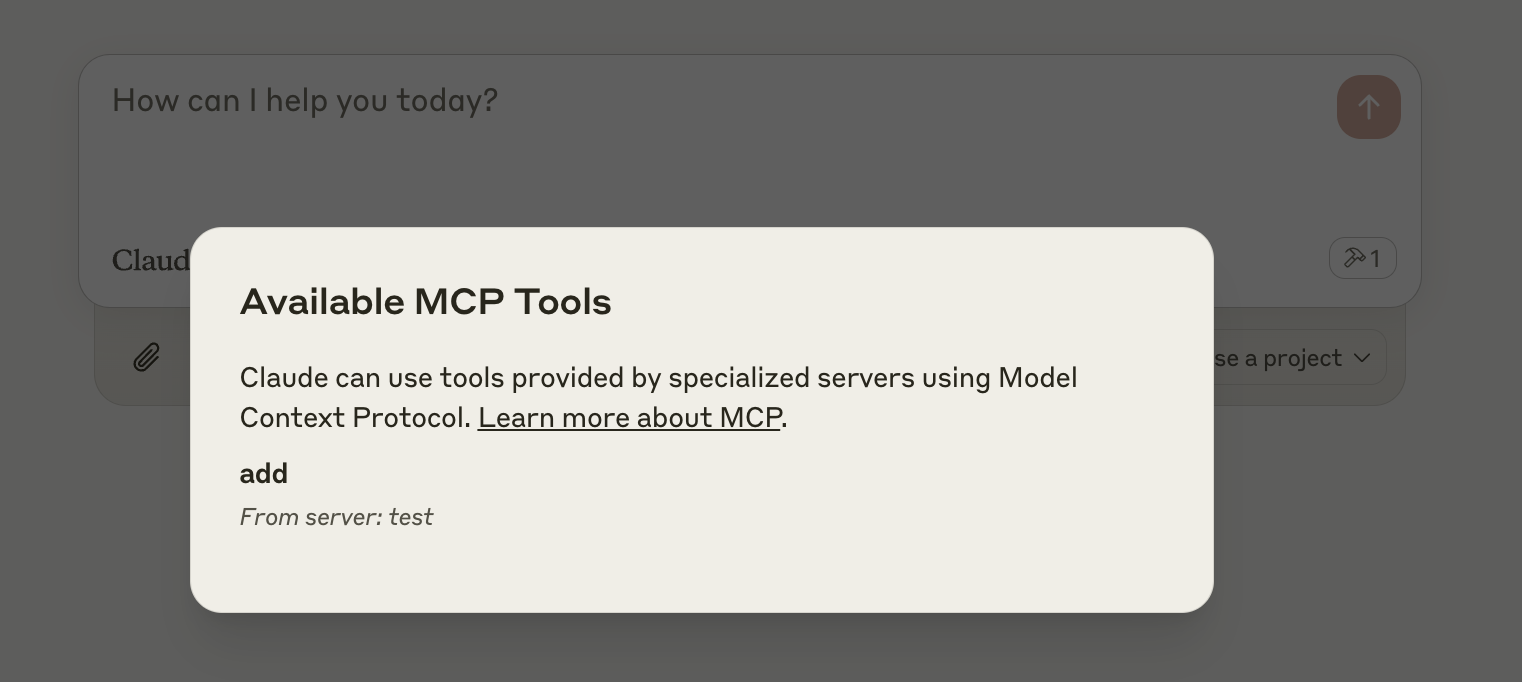
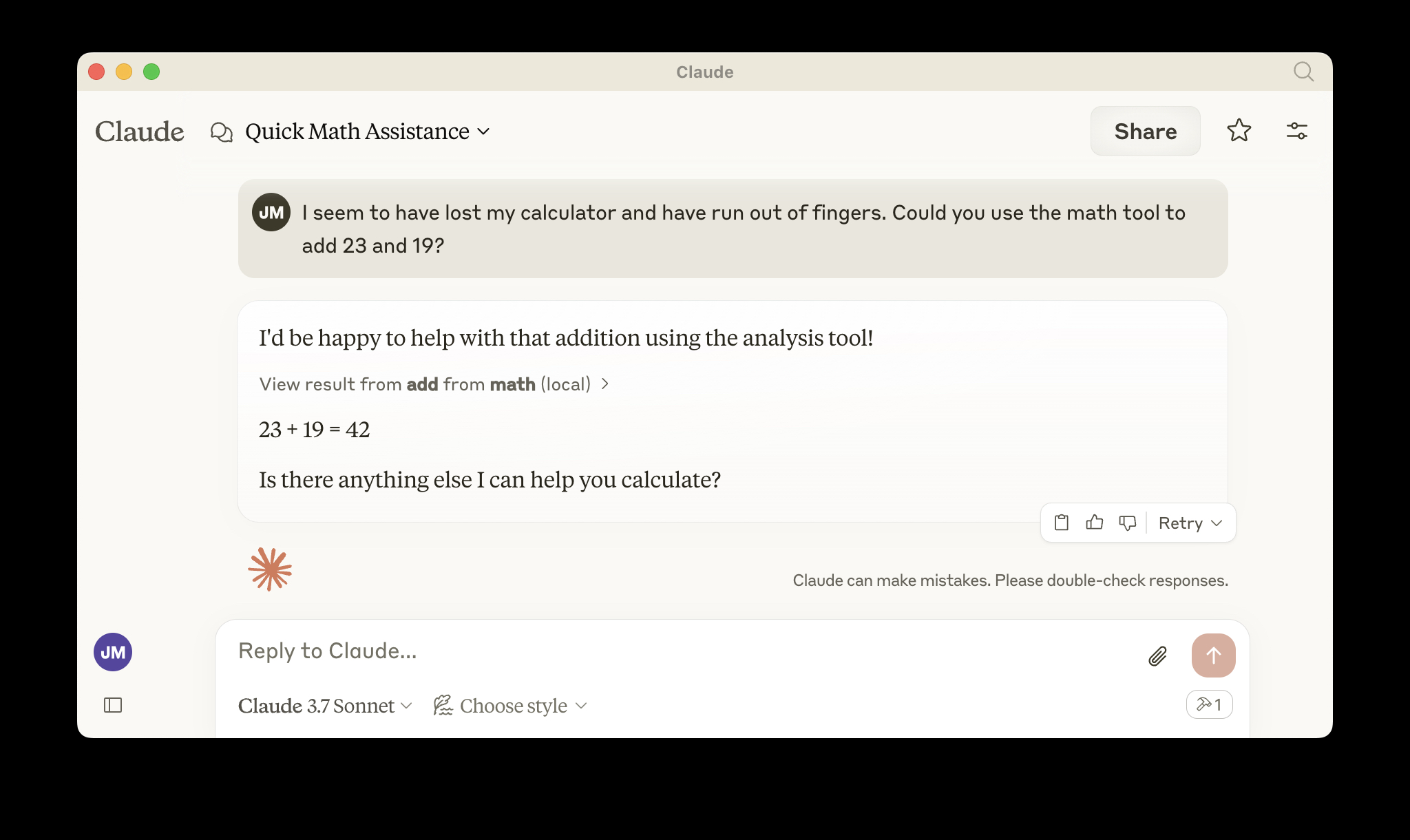
When you open Claude a browser window should open and allow you to login. You should see the tools available in the bottom right. Given the right prompt Claude should ask to call the tool.
Deploy to Cloudflare
npx wrangler kv namespace create OAUTH_KV- Follow the guidance to add the kv namespace ID to
wrangler.jsonc npm run deploy
Call your newly deployed remote MCP server from a remote MCP client
Just like you did above in "Develop locally", run the MCP inspector:
npx @modelcontextprotocol/inspector@latest
Then enter the workers.dev URL (ex: worker-name.account-name.workers.dev/sse) of your Worker in the inspector as the URL of the MCP server to connect to, and click "Connect".
You've now connected to your MCP server from a remote MCP client.
Connect Claude Desktop to your remote MCP server
Update the Claude configuration file to point to your workers.dev URL (ex: worker-name.account-name.workers.dev/sse) and restart Claude
{
"mcpServers": {
"math": {
"command": "npx",
"args": [
"mcp-remote",
"https://worker-name.account-name.workers.dev/sse"
]
}
}
}
Debugging
Should anything go wrong it can be helpful to restart Claude, or to try connecting directly to your MCP server on the command line with the following command.
npx mcp-remote http://localhost:8787/sse
In some rare cases it may help to clear the files added to ~/.mcp-auth
rm -rf ~/.mcp-auth
Servidores relacionados
Brex
Interact with the Brex API to manage financial data and resources.
Remote MCP Server on Cloudflare
A remote MCP server deployable on Cloudflare Workers with OAuth login support, using Cloudflare KV for data storage.
Bybit MCP Server
Access Bybit's v5 API for real-time market data, trading operations, and account information.
Financial Data
Provides access to real-time and historical stock data from the Alpha Vantage API.
Middleware MCP Server
Interact with Middleware to monitor infrastructure, logs, metrics, and traces via the MCP protocol.
Apillon MCP Server
Interact with Apillon's Storage, Hosting, and NFT modules.
Rewards Flights Public MCP
Deploy a remote, authentication-free MCP server on Cloudflare Workers to search for rewards flights.
HuggingFace Spaces
Server for using HuggingFace Spaces, supporting Images, Audio, Text and more. Claude Desktop mode for ease-of-use.
OKX MCP Server
Provides real-time cryptocurrency price data from the OKX exchange.
ConvertAPI MCP Hosted Server
ConvertAPI MCP Hosted Server exposes document converters and tools as discoverable tools for MCP-compatible AI clients using OAuth for authentication.